ISMS software
ISMS software is onmisbaar voor organisaties die gestructureerd willen voldoen aan normen zoals ISO 27001, NEN 7510 en BIO.
Met ISMS software centraliseer je alle informatiebeveiligingsprocessen in één overzichtelijk platform, waardoor compliance geen versnipperde inspanning meer is. ISMS software helpt organisaties risico’s systematisch te identificeren, analyseren en beheersen, wat essentieel is voor aantoonbare naleving. Door gebruik te maken van ISMS software wordt het beheren van beleid, maatregelen en controles aanzienlijk efficiënter en minder foutgevoelig. Daarnaast ondersteunt ISMS software continue monitoring en verbetering, wat perfect aansluit bij de PDCA-cyclus die deze normen vereisen.
Organisaties kunnen met ISMS software eenvoudig audits voorbereiden en uitvoeren, doordat alle relevante documentatie direct beschikbaar is. Dit zorgt niet alleen voor tijdswinst, maar verhoogt ook de betrouwbaarheid en consistentie van de informatievoorziening. ISMS software biedt bovendien inzichtelijke dashboards en rapportages, waardoor management direct kan sturen op risico’s en compliance.
Voor sectoren zoals zorg en overheid, waar NEN 7510 en BIO verplichtingen stellen, maakt ISMS software het verschil tussen reactief en proactief beveiligingsbeheer.
Het gebruik van ISMS software verlaagt de administratieve lasten en verhoogt tegelijkertijd de kwaliteit van informatiebeveiliging. Hierdoor ontstaat er een solide fundament voor vertrouwen bij klanten, partners en toezichthouders.
Kortom, ISMS software transformeert compliance van een complexe verplichting naar een strategisch voordeel voor de organisatie. Met een duidelijk concept.
ISMS software, waar op letten
Enkele punten, die belangrijk zijn om op te letten:
- Certificering
Kijk of het ISMS in een certificeringstraject goed bruikbaar is
- Aanpasbaarheid
Zorg ervoor dat het systeem aanpasbaar is aan de specifieke eisen van jouw organisatie.
- Integratie
Het ISMS moet in staat zijn om de verschillende aspecten binnen het managementsysteem te integreren
- Beveiligingsfuncties
Controleer of het ISMS beveiligingsfuncties heeft zoals toegangscontrole (eventueel 2FA), rollenstructuur, georedundantie.
- Gebruiksvriendelijkheid
Kijk of het ISMS eenvoudig te gebruiken is voor zowel IT-beheerders als gebruikers.
- Ondersteuning en updates
Zorg ervoor dat het ISMS ondersteuning biedt en regelmatig updates ontvangt om de beveiliging en functionaliteit up-to-date te houden.
ISMS aandachtsgebieden
Om te voldoen aan de managementsysteem normen voor informatiebeveiliging moet een organisatie een volledig managementsysteem (ISMS - Information Security Management System) hebben met beheersmaatregelen t.a.v. informatiebeveiliging. De aandachtsgebieden zijn:
- beveiligingsbeleid
- beheer van bedrijfsmiddelen
- personeel
- fysieke beveiliging
- beheer communicatieprocessen
- beheer van bedieningsprocessen
- toegangsbeleid
- informatiesystemen
- incidentenbeheer
- bedrijfscontinuïteitsbeheer
- naleving
Meer weten dan alleen zo'n opsomming, dan kan je terecht bij onze business partner Meta-audit.nl. Zij weten ook wat de verplichte documenten zijn, klik dan hier.
Let op: de ISO 27001 is veranderd, ISO 27001:2022. En voor de NEN 7510 geldt hetzelfde: NEN 7510:2024. Onze collega's van Meta-audit.nl weten er meer van. Klik hier voor hun Quickstart implementatie ISO 27001:2022.
Nieuw: in samenwerking met Meta-audit.nl is er een ISMS starterspakket (conform ISO 27001:2022 / NEN 7510:2024 - verplichte documenten / registraties) na de proefperiode van het Metaware managementsysteem beschikbaar. Contact ons voor meer info.
ISMS, risico-gebaseerd
De beheersing van de informatiebeveiliging moet zijn gebaseerd op de onderkende risico's. Risico beheersing is daarmee een integraal onderdeel: risico's identificeren, classificeren en vervolgens met maatregelen deze risico's mitigeren (verminderen). Gaandeweg zal het het aantal geïdentificeerde risico's echter snel toenemen en dus typisch iets om NIET in een spreadsheet bij te houden, maar in een workflow tool. Zo blijft het risicobehandelplan actueel en weten alle betrokkenen wie wat wanneer moet doen.
ISMS, control framework
Het ISMS bevat een groot aantal beheersmaatregelen die moeten zijn geïmplementeerd. Het geheel van beheersmaatregelen wordt ook wel control framework genoemd.
Deze beheersmaatregelen moeten duidelijk aantoonbaar effectief zijn en zijn dan ook een belangrijk onderwerp in elke audit. Een tool maakt de status van zo'n control framework inzichtelijk.
ISMS, opzetten
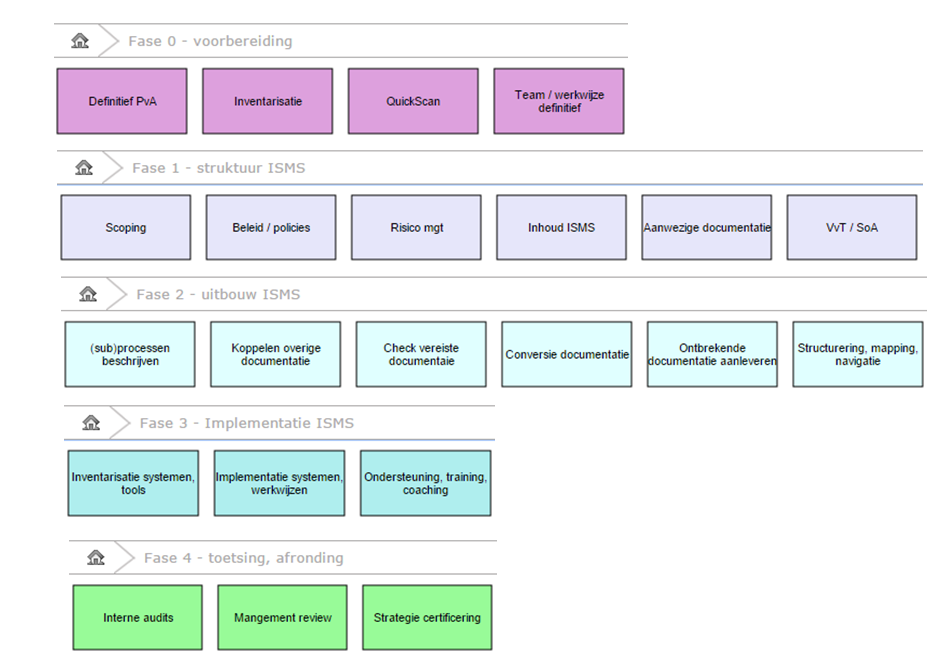
Het opzetten van een ISMS is best wel een klus waarvoor een duidelijk stappenplan nodig is, ondersteund door de software tool.
De implementatie is opgesplitst in 5 fases:
- Voorbereiding
- Structuur ISMS
- Uitbouw ISMS
- Implementatie ISMS
- Toetsing, afronding
ISMS, praktisch voorbeeld
Met hulp van onze business partner Meta-audit.nl hebben we een demo-omgeving ingericht. Zie ook hun overzichten en de verplichte documenten.
Klik op de afbeeldingen voor de demo-omgeving.
Wil je sneller van start? Zet dan een managementsysteem als cloudoplossing in 60 sekonden klaar !
|
Metaware platform
Kenmerk
- Volledig geïntegreerd en modulair ISMS platform
- Direct inzetbare SAAS soevereine cloud software
- Ondersteund gangbare normen voor informatiebeveiliging als ISO 27001, BIO en NEN 7510
Drijfveer
- Totaalbeeld van borging versus realisaties
- Aantoonbare compliance in een control framework
- Consistentie in risicobeheersing
Beslissingsfactor
- Hoog gebruikersgemak door visuele navigatie en heldere interfaces
- Vriendelijk licentiemodel o.b.v. kerngebruikers
|
