Cyberveiligheid control framework
Uit het kenniscentrum van Metaware.
Zoekwoorden: Cyberveiligheid control framework, cybersecurity control framework, control framework ISO 27001, control framework, beheerssysteem, beheersmaatregelen, audit, compliance, ISO27001, kwaliteit, managementsysteem, NEN7510, BIO, AVG, GDPR
Cyberveiligheid control framework
Een cyberveiligheid control framework is een gestructureerd geheel van beheersmaatregelen bedoeld om risico’s op het gebied van digitale dreigingen te beheersen. Het biedt organisaties richtlijnen om hun informatiebeveiliging systematisch en aantoonbaar te organiseren. Een cyberveiligheid control framework bevat zowel technische als organisatorische controls, zoals toegangsbeheer, incidentrespons en beveiligingsbeleid. Door het gebruik van zo’n framework kunnen bedrijven hun beveiligingsmaatregelen afstemmen op risico’s, wetgeving en best practices. ISO27001 is een internationaal erkende norm die een managementsysteem voor informatiebeveiliging beschrijft, en vormt vaak de basis voor een effectief cyberveiligheid control framework. ISO27001 specificeert welke beleidsmaatregelen en processen nodig zijn om vertrouwelijkheid, integriteit en beschikbaarheid van informatie te garanderen. Een cyberveiligheid control framework gebaseerd op ISO27001 maakt het mogelijk om risico’s proactief te identificeren, evalueren en beperken. Organisaties gebruiken het framework ook om compliance met regelgeving, zoals GDPR of NIS2, te borgen. Het structureert audits en interne controles, waardoor beheersing aantoonbaar wordt. Een goed geïmplementeerd cyberveiligheid control framework bevordert vertrouwen bij klanten, toezichthouders en partners.
Control framework ISO 27001
Een control framework voor ISO 27001 (versie 2022) biedt een gestructureerde aanpak om de beheersmaatregelen (controls) die in deze norm worden voorgeschreven effectief te implementeren, te beheren en te monitoren. De ISO 27001-norm is een internationale standaard voor informatiebeveiligingsmanagementsystemen (ISMS) en heeft tot doel organisaties te helpen bij het beschermen van hun informatie en het minimaliseren van risico’s op gebied van cyberveiligheid en gegevensbescherming. De recente update naar ISO 27001:2022 brengt enkele nieuwe en herschikte beheersmaatregelen met zich mee, waardoor een goed opgezet control framework belangrijker is dan ooit voor een effectieve implementatie en naleving.
Belangrijkste elementen van een control framework voor ISO 27001:2022:
1. Risicobeoordeling en -beheer
De basis van een control framework ISO 27001 is risicomanagement. Het control framework begint daarom met een systematische benadering van risicobeoordeling. Het framework moet helpen om:
- Risico’s te identificeren en te evalueren (waar zitten de kwetsbaarheden, bedreigingen en hun impact?).
- Risicocriteria vast te stellen (wanneer is een risico aanvaardbaar of onaanvaardbaar?).
- Maatregelen te definiëren om geïdentificeerde risico’s te mitigeren.
Dit helpt organisaties om risico's op een consistente manier te beoordelen en prioriteit te geven aan de beveiligingsmaatregelen die het belangrijkst zijn.
2. Structuur van het control framework
Een effectief control framework ISO 27001 is opgebouwd rond de 93 controls die in Bijlage A van ISO 27001:2022 zijn opgenomen. Deze zijn verdeeld in vier thema's:
- Organisatorische maatregelen (bijvoorbeeld beleid, rollen en verantwoordelijkheden)
- Mensenmaatregelen (zoals beveiligingsbewustzijn en training)
- Fysieke maatregelen (zoals beveiliging van gebouwen en apparatuur)
- Technische maatregelen (zoals encryptie, toegangsbeheer en logging)
Voor elke maatregel wordt een plan opgesteld dat beschrijft:
- De exacte beheersmaatregel.
- De vereiste technische of organisatorische oplossingen.
- Wie verantwoordelijk is voor implementatie, naleving en periodieke controles.
3. Beleid en procedures
Het framework moet een set van beleid en procedures bevatten die voldoen aan de eisen van ISO 27001 en de dagelijkse werking van de organisatie ondersteunen. Dit zijn bijvoorbeeld:
- Informatiebeveiligingsbeleid.
- Richtlijnen voor toegangsbeheer.
- Procedures voor incidentmanagement.
- Procedures voor continue verbetering.
Deze documentatie biedt medewerkers richtlijnen en zorgt voor consistentie in de uitvoering van beveiligingsmaatregelen.
4. Toewijzing van rollen en verantwoordelijkheden
Om de effectiviteit van de beheersmaatregelen te waarborgen, moet het framework duidelijke rollen en verantwoordelijkheden definiëren. Dit omvat:
- Een Chief Information Security Officer (CISO) / Security Officer (SO) of een verantwoordelijke voor informatiebeveiliging.
- Risico-eigenaren die verantwoordelijk zijn voor specifieke risico’s binnen hun domein.
- Technische en operationele teams die controles uitvoeren en bijhouden.
- Heldere toewijzing zorgt voor accountability en voorkomt dat maatregelen niet worden opgevolgd.
5. Monitoring en rapportage
Een belangrijk onderdeel van het control framework is het monitoren van de effectiviteit van beheersmaatregelen. Dit omvat:
- Het uitvoeren van periodieke controles en audits (intern of door derden).
- Monitoring van afwijkingen en incidenten.
- Regelmatige risicobeoordelingen om veranderingen in de organisatie of in het dreigingslandschap te detecteren.
De resultaten van deze controles worden gerapporteerd aan het management en vormen de basis voor voortdurende verbetering van het ISMS.
6. Training en bewustzijn
ISO 27001 stelt dat alle betrokkenen zich bewust moeten zijn van hun rol in de informatiebeveiliging. Het framework moet daarom ook training- en bewustwordingsprogramma's omvatten.
Dit kan bestaan uit:
- Reguliere trainingen en refreshers voor medewerkers over informatiebeveiliging.
- Specifieke trainingen voor IT-personeel op het gebied van beveiliging.
- Campagnes om de algemene beveiligingscultuur te versterken.
7. Incidentmanagement en herstelmaatregelen
Het framework moet een proces bevatten voor het identificeren, rapporteren en oplossen van beveiligingsincidenten.
Dit omvat:
- Het opzetten van een incident response team.
- Procedures voor snelle escalatie en opvolging van incidenten.
- Een plan voor herstel en continue verbetering om lessen uit incidenten toe te passen.
8. Continue verbetering
ISO 27001:2022 vereist een cyclus van continue verbetering om te garanderen dat het ISMS zich aanpast aan nieuwe bedreigingen en vereisten. Dit houdt in dat:
- Het framework regelmatig wordt herzien en aangepast.
- Er lessen worden getrokken uit audits, incidenten en nieuwe risicoanalyses.
- Verbeteringen systematisch worden toegepast, bijvoorbeeld met behulp van de PDCA-cyclus (Plan-Do-Check-Act).
- Implementatieoverwegingen
Een goed opgezet control framework moet flexibel en schaalbaar zijn, zodat het meegroeit met de organisatie en aansluit bij zowel technologische als operationele veranderingen. Daarnaast is het essentieel om periodieke evaluaties en controles uit te voeren om te zorgen dat de beheersmaatregelen effectief blijven en in lijn zijn met de actuele bedrijfs- en risicocontouren.
Conclusie
Een control framework voor ISO 27001:2022 is meer dan alleen een verzameling technische maatregelen. Het is een holistische aanpak die beleid, procedures, rollen, training en technische controls combineert om informatiebeveiliging integraal en effectief te waarborgen. Met een goed ingericht control framework kan een organisatie zich niet alleen certificeren volgens ISO 27001, maar ook haar beveiligingshouding structureel versterken en risico’s proactief beheersen.
Control framework ISO 27001 voorbeeld
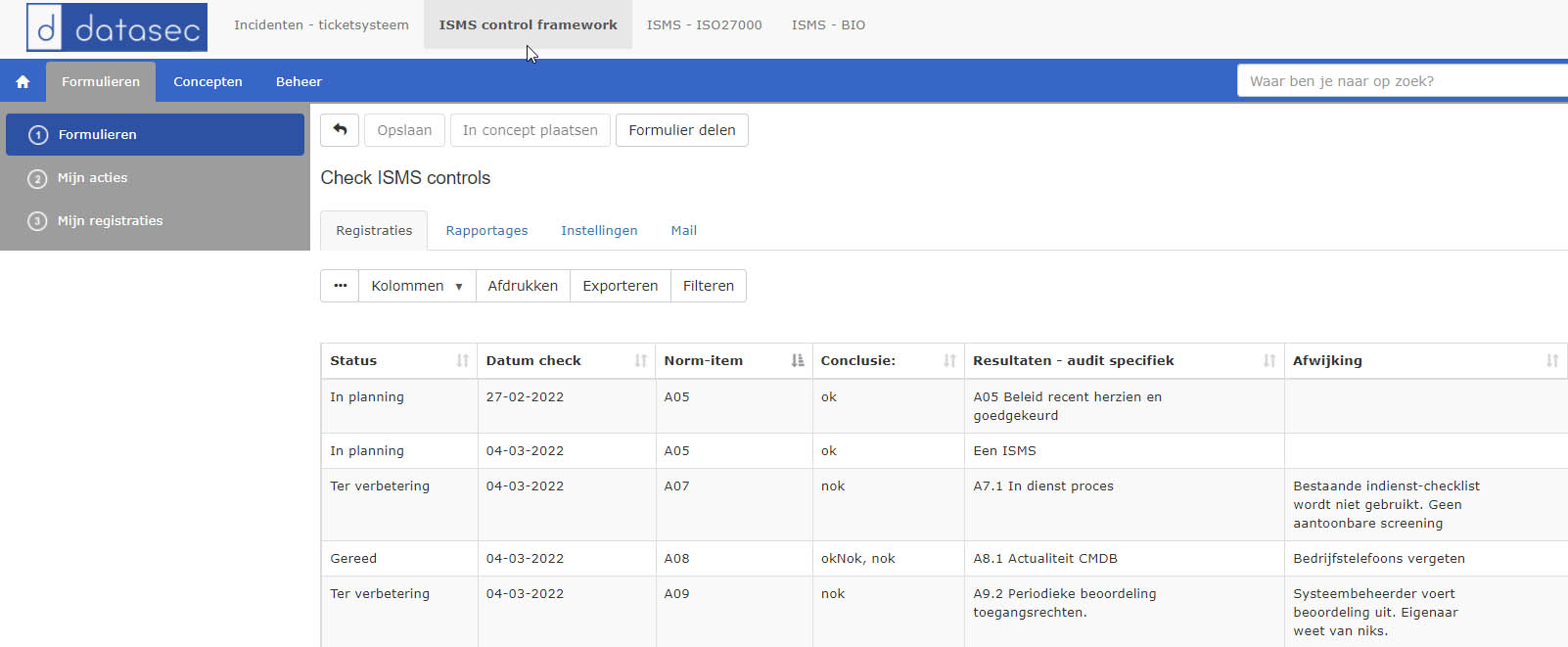
Als voorbeeld is een ISMS -Information Security Management System- control framework uitgewerkt, gericht op de ISO 27001, Annex A. Een set van 95 beheersmaatregelen gericht op informatiebeveiliging, indien van toepassing.
Binnen het managementsysteem platform is het ISMS control framework een onderdeel. Periodiek wordt hier vastgelegd wat de toetsingsresultaten van de effectiviteitscontroles van de betreffende beheersmaatregelen (controls) zijn. Groot voordeel is dat er directe links met het beschreven managementsysteem en de verschillende kwaliteitsregistraties of KPI-metingen zijn.
Klik hier voor het ISO 27001:2022 ISMS control framework van onze business partner meta-audit.nl

Business partners
Metaware werkt graag samen met kundige adviseurs. Wij leveren de tools -het managementsysteem platform- en onze business partners hebben de inhoudelijke kennis, elk kundig op hun eigen gebied. Of het nu ISO27001, COSO, ISAE3402, COBIT, BIO, NEN7510, AVG, GDPR of een ander control framework is.